I created this cheatsheet to help me remember some useful kvm commands. There are two versions, the simplest one and the extended one. Commands shown in the cheatsheet are not all the existent ones, so please, read the documentation for more info.
Category Archives: System Administration

Citrix XenCenter process hang when importing VMDK
Recently I tried to import a VMDK disc into a new VM using the old and commercial Citrix XenCenter 6.2 (build 1069). It created a process that hanged and a virtual machine kept running in the background.
I started the import process and selected DHCP as network configuration mode for the process of importing when I had no DHCP configured on the particular VLAN. This caused that the import process to get blocked and later it failed. Everything was fine until the network guy told me that he was receiving alerts from his switch that a certain MAC was trying to get IP by DHCP.
I checked in XenCenter all the VM’s and didn’t found the MAC. The mac was neither in the host.
Here is what I did:
Is the MAC assigned to your virtual switch?:
Which is the VM assigned to this MAC?:
..
{"Interface":{"6efaab55-947f-48c5-906f-6012cb0062de":{"external_ids":["map",[["attached-mac","66:6e:f9:7f:ac:9b"],["iface-id","8c2708ff-4d45-01e4-1ec3-04225d5247d1"],["iface-status","active"],["xs-network-uuid","f79523b2-efa6-5a2a-df3e-859b42fbc9a5"],["xs-vif-uuid","8c2708ff-4d45-01e4-1ec3-04225d5247d1"],["xs-vm-uuid","071e54a2-0b3b-5e61-1f84-1f3575e49f8f"]]]}},"_date":1440508017}
..
Which is the name of the VM with this UID?:
..
uuid ( RO) : 071e54a2-0b3b-5e61-1f84-1f3575e49f8f
name-label ( RW): Transfer VM for VDI b660621f-6eeb-4e61-b2b4-a33a3b14c46b
power-state ( RO): running
...
Get more info about 071e54a2-0b3b-5e61-1f84-1f3575e49f8f:
Find the VDI:
[codesyntax lang="bash" lines="no" container="none" blockstate="expanded"]
[root@xenserver /]# xe vdi-list
uuid ( RO) : b660621f-6eeb-4e61-b2b4-a33a3b14c46b
name-label ( RW): Virtual Disk
name-description ( RW): Created by XenCenter Disk Image Import
sr-uuid ( RO): a2a537a6-10ce-15ad-389d-a8c54a5f2bc3
virtual-size ( RO): 32212254720
sharable ( RO): false
read-only ( RO): false
More info about the VDI:
uuid ( RO) : 70185847-43a5-b9c6-2964-f737f24f6e38
vm-uuid ( RO): 071e54a2-0b3b-5e61-1f84-1f3575e49f8f
vm-name-label ( RO): Transfer VM for VDI b660621f-6eeb-4e61-b2b4-a33a3b14c46b
vdi-uuid ( RO): b660621f-6eeb-4e61-b2b4-a33a3b14c46b
empty ( RO): false
device ( RO): xvdb
Stop&destroy the machine:
[root@xenserver /]# xe vm-destroy uuid=071e54a2-0b3b-5e61-1f84-1f3575e49f8f
Tivoli TSM 7.1.1 database instance UML schema
I wanted to create some UML schemas for my understanding about Tivoli TSM internals.I couldn’t find any schema in IBM neither in the internet, so I created a simple script that, given a list of “table_name, column, type”, creates a very basic Gnome DIA diagram.
The query to create the input file for my script is:
or if you want only the tables for TSM Instance and not internal the tables for internal schemas:
Feel free to download and test the script. Call the input file “taules_columnes_tsm3” or modify dbdump variable in genera_tot() function. I didn’t tune it so its ugly but you can improve it if you want in a few minutes.
Download the script and the generated .dia from here:
generador_tsm_uml.sh
TSM_7.1.1_database_schema.dia
Extract a Backtrace from a Running Daemon
More Information
http://www.bonsai.com/wiki/howtos/debugging/daemon_backtrace/
GDB Documentation
Attach to the daemon with gdb
IMPORTANT NOTES:
- You’ll need to be root (or the owner of the daemon process).
- You’ll want to do this first part “briskly” since the daemon will be stopped until you give the “continue” command.
- This is reasonably invasive; be prepared to restart the daemon if something goes wrong.
Continue reading
Using GNU/Linux Alternatives – Java, Javaws and Java Plugin example
In this post I’ll briefly show an use case of Alternatives command available in Fedora, Ubuntu, Debian, and other GNU/Linux flavours.
alternatives – maintain symbolic links determining default commands
Add custom application link to Gnome3 Activities Menu
If you want to create a custom link to some command or application on the Gnome3 activities menu, and you don’t want to install tools like Alacarte, just do the following:
1. Create a <name>.desktop in ~/.local/share/applications/
[lipi@i5-moll applications]$ pwd
/home/lipi/.local/share/applications
[lipi@i5-moll applications]$ cat oracle-task-input.desktop
[Desktop Entry]
Type=Application
Name=Oracle Task Input
Comment=Llança el gestor de tasques Oracle
Exec=/home/lipi/projects/task_management.sh
Icon=/home/lipi/projects/oracle-icon.png
Terminal=false
Encoding=UTF-8And that’s all!
If you want to see the icons that are defined in the system, take a look into /usr/share/applications/
How to lock access to system control on Fedora 19+
Recently I wanted to make a “black-box” style laptop limiting access to a non-privileged Linux user to only insert characters with the keyboard, this is: no ctrl+alt+del, only one tty, no graphical environment, no action for power, suspend, and other laptop buttons, no mouse, … so, only the keyboard input.
It is a very very easy thing.
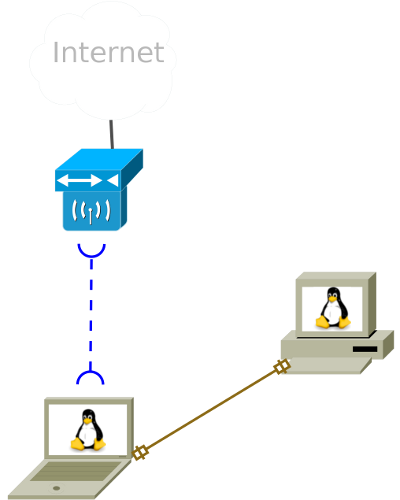
How to share Internet Connection with GNU/Linux
You just need to setup some iptables rules and turn on the ip_forward feature in the Linux kernel, assign some IPs and Routes and voila, your PC will become a router.
For example, suppose you have a laptop connected to Internet through a wifi card (let’s call it eth1) and you want to connect a PC to Internet through it, using an ethernet cable.
Coprocess in shell
This article is pending and will talk about coprocesses used in shells.
A coprocess is a process run asynchronously on a shell that has a pipe for stdin, stderr, stdout, etc. attached to the main process. By this way you are able for example to redirect a main process output both to a log and to stdout at the same time.
http://www.gnu.org/software/bash/manual/html_node/Coprocesses.html
http://www.linuxjournal.com/content/bash-co-processes
http://www.gnu.org/software/bash/manual/html_node/Redirections.html#Redirections
http://www.dartmouth.edu/~rc/classes/ksh/coprocesses.html
http://wiki.bash-hackers.org/syntax/keywords/coproc
Basic Unix System Monitoring Commands
This post is a cheat to remember which are the main commands to find usage of your consumed resources on a Unix machine.